Key takeaways
Here are the key insights from our website breakdown analysis of Okta.
Okta’s homepage clarifies scope fast by framing identity as a universal control plane for employees, customers, partners, and AI agents, then reinforcing it with product “platform” segmentation (Okta Platform vs Auth0 Platform).
Conversion paths are intentionally split between “Start a free trial” and “Contact sales,” which fits enterprise security buying behavior and reduces friction for both self-serve evaluators and procurement-led deals.
The navigation and solution taxonomy are built for complex identity use cases, using identity types (Workforce, Customer, AI Agent, Non-Human) and industry groupings to shorten time-to-relevance for regulated buyers.
Okta uses quantified customer stories (e.g., “100M users,” “1,500 applications,” “211% ROI”) as the primary proof mechanic, which increases credibility for high-stakes IAM decisions.
The site positions Okta as a “neutral, extensible platform,” a competitive wedge against suite vendors, and backs it with ecosystem language like Okta Integration Network and developer portals.
Trust is treated as a first-class product attribute, with a dedicated “Trust” area, platform status links (Okta Platform Status, Auth0 Status), and enterprise governance/security modules prominently listed.
Home
Okta’s homepage works because it frames identity as a single, expandable layer that can secure humans and machines—then immediately gives visitors two clear next steps: Get started (trial) or Contact sales.
What’s happening above the fold
The hero message (“Secure Identity for Employees, Customers, and AI”) sets a broad category claim, while the supporting line (“Okta secures AI and every other identity, from machine to human”) modernizes IAM positioning around agentic systems. The page also uses a time-bound event strip (Okta Showcase RSVP; streaming live March 16th) to create urgency without interfering with core CTAs.
Information architecture that matches the buying journey
Okta leans on a large, enterprise-grade mega-menu with explicit segmentation:
- Platforms: Okta Platform vs Auth0 Platform (clear separation of workforce IAM vs customer identity developer use cases).
- Identity types: Workforce Identity, Customer Identity, AI Agent Identities, Non-Human Identities.
- Modules: Single Sign-On, Adaptive MFA, Universal Directory, Privileged Access Management, Identity Threat Detection & Response.
This structure is a practical “self-qualification” system: security leaders can map their program scope; developers can jump straight to documentation; procurement can go to pricing.
Design and messaging patterns that reduce risk perception
The homepage reinforces credibility through recognizable enterprise patterns: prominent phone number (+1 800…), “neutral and extensible platform” language, and repeated entry points to Free Trial and Pricing. It also anchors the narrative in an “identity security fabric” concept—useful for positioning against Microsoft Entra ID or Ping Identity—while still showing concrete solution pages for each capability.
Key terms: identity security fabric, AI agents, neutral platform, Free Trial, Contact sales.
Pricing
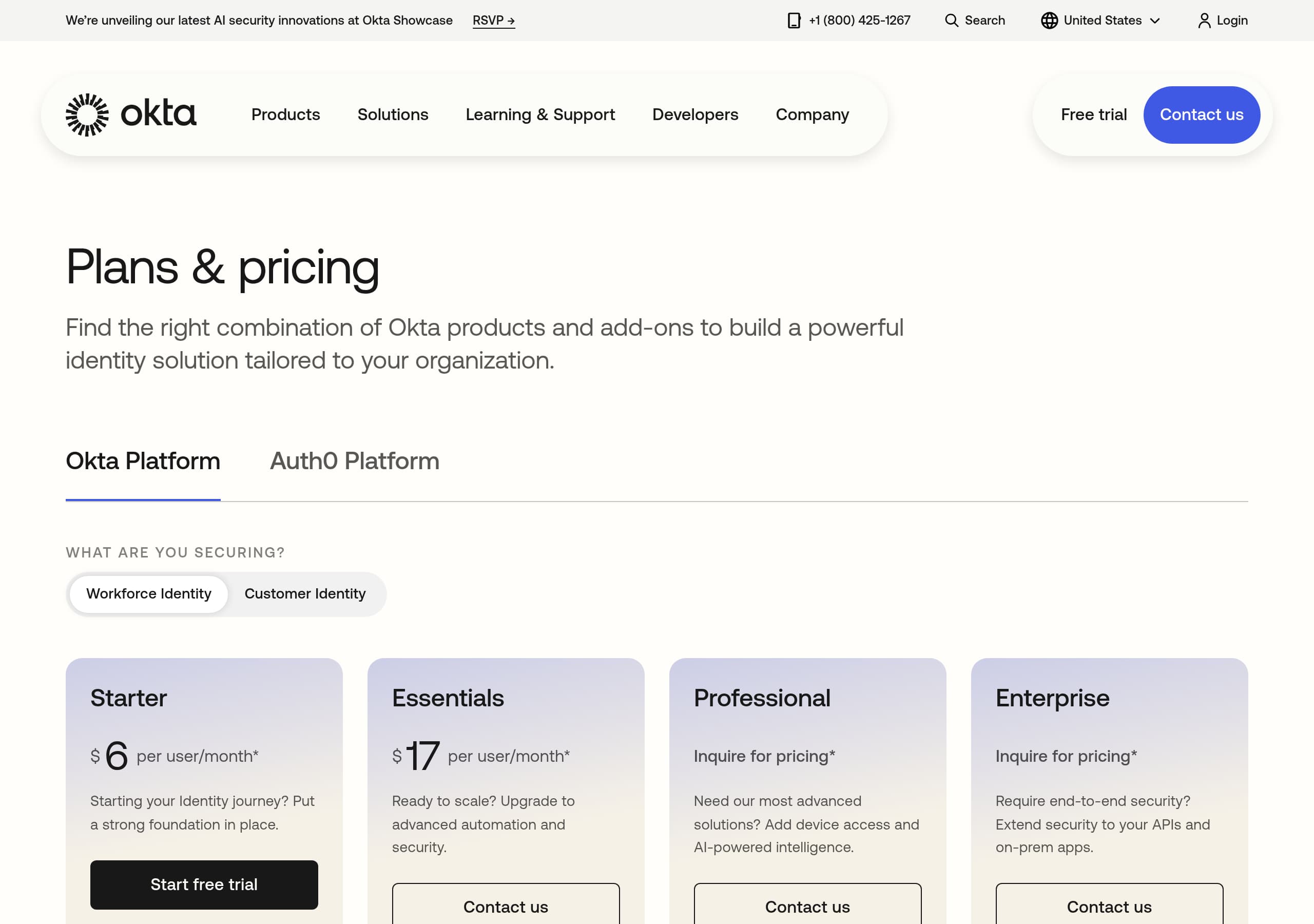
Okta’s pricing experience is structured to handle two realities at once: self-serve evaluation (trial-first) and enterprise buying (quote-driven), which is typical for Identity and Access Management.
What the pricing page is optimizing for
From the navigation and repeated “Pricing” entry points, Okta treats pricing as a high-intent destination, but the site’s overall conversion design suggests pricing is not purely “add to cart.” Instead, Okta keeps strong parallel CTAs—Start a free trial and Contact sales—to support both smaller teams testing SSO/MFA and large organizations that need governance, advanced security, and contractual terms.
Packaging signals from the product taxonomy
Even before you land on the pricing page, the product list previews how packaging likely works:
- Core workforce modules: Single Sign-On, Adaptive MFA, Universal Directory.
- Advanced controls: Privileged Access Management, Identity Threat Detection & Response, Identity Security Posture Management.
- Governance: Lifecycle Management and Identity Governance.
- Customer identity: Auth0 and “Okta Customer Identity.”
This modular architecture typically translates to “per-user / per-month” building blocks and enterprise bundles—especially when governance and threat protection are involved.
Why this is effective for enterprise conversion
Okta’s pricing posture reduces friction in three ways:
- It avoids forcing complex buyers into a single number when requirements vary (apps count, workforce size, B2C MAUs, admin roles).
- It encourages commitment-light evaluation via the 30-day free trial.
- It preserves a direct path to procurement with “Contact sales,” plus visible phone support.
The key improvement opportunity is clarity: if the pricing page requires too much scrolling or gating to see starting prices, it can push smaller customers to alternatives like JumpCloud or Microsoft Entra ID. Clear “starting at” anchors and a simple comparison table would further strengthen pricing transparency.
Key terms: Pricing, Contact sales, 30-day free trial, workforce identity, customer identity.
Features
Okta’s features presentation succeeds by balancing a platform narrative (“identity security fabric”) with a clear module list that maps to real IAM programs.
Platform-first framing
Two platform cards anchor the product story:
- “Okta: Secure all of your identities within an identity security fabric.”
- “Auth0: Ship amazing experiences with enterprise-grade customer identity.”
This is an effective split because workforce IAM and CIAM buyers have different success criteria (IT governance vs developer experience, MAU scale, fraud controls).
Feature coverage is explicit and comprehensive
Okta’s mega-menu functions as a feature index, which is useful for enterprise evaluators who want to confirm requirements fast. Notable modules called out:
- Single Sign-On and Adaptive MFA (baseline access controls).
- Device Access and Access Gateway (device and legacy app coverage).
- Universal Directory (identity source-of-truth positioning).
- Privileged Access Management + Privileged Access Identity (PAM adjacency).
- Identity Threat Detection & Response and Identity Threat Protection (security operations integration).
- Lifecycle Management and Identity Governance (joiner/mover/leaver + access reviews).
- Okta Integration Network (ecosystem and pre-built integrations).
Modern wedge: AI agent security
Okta is actively differentiating with “Agentic AI Security,” “Okta for AI Agents,” “Auth0 for AI Agents,” and “Cross App Access Protocol.” This creates a forward-looking category hook while still fitting into identity fundamentals (authN/authZ, lifecycle, monitoring). The phrase “secure the identity of every AI agent across its full lifecycle” reads like a feature promise that CISOs can translate into policy, inventory, and control requirements.
A practical improvement would be a tighter feature comparison between Okta Platform vs Auth0 Platform (what’s shared, what’s distinct), but the current feature taxonomy already makes the breadth legible.
Key terms: Single Sign-On, Adaptive MFA, Identity Governance, Okta Integration Network, AI agent security.
Signup
Okta’s signup strategy is intentionally multi-lane: it supports hands-on evaluation via a 30-day free trial while maintaining a high-touch route for enterprise complexity through Contact sales.
Primary conversion paths visible on the homepage
The page repeatedly surfaces:
- “Start a free trial” (explicitly labeled as a 30-day free trial to set expectations).
- “Talk to an expert” and “Contact sales,” including a phone number and an email option.
This is a strong fit for Okta’s market because IAM trials often require integration (IdPs, apps, directories) and buyers may need solution design early.
Funnel support for different personas
Okta’s global navigation includes persona-oriented destinations:
- Developers (Developer Center, product documentation, marketplaces, status pages).
- Learning & Support (Support Center, Product Training, Product Certification).
- Solutions by industry and identity type.
That means the “signup” experience is not only the trial form—it’s the broader onboarding ecosystem that reduces time-to-first-value after account creation.
Onboarding confidence mechanisms
The site reduces perceived risk during signup by providing:
- Direct access to Okta Platform Status and Auth0 Status (operational transparency).
- Professional Services and Success Plans (signals that implementation is supported).
- Extensive resources (webinars, Identity 101, release overviews) that help evaluators build internal consensus.
Where Okta could improve conversion is tighter continuity between the CTA and the next step: explicitly stating what the trial includes (which modules, integration limits, admin seats) and whether the trial is for Okta Platform, Auth0, or both. For high-intent visitors, a short “3-step” preview (Create account → Connect directory/app → Enforce MFA) would make onboarding feel faster.
Key terms: 30-day free trial, Contact sales, Developer Center, Product Training, Status pages.
Trust
Okta’s trust posture is communicated through both explicit trust navigation and implicit enterprise cues like transparency, governance modules, and analyst validation.
Trust is built into the site map
Okta includes a dedicated “Trust” area under Company, alongside “Secure Identity Commitment” and “Accessibility.” This matters in security buying because evaluators look for vendor posture signals (policies, commitments, disclosures) before they ever request a quote.
Operational transparency and reliability cues
Two visible elements do a lot of work:
- Links to Okta Platform Status and Auth0 Status from the Developers area.
- A global enterprise support posture: Support Center, Knowledge Base, Product Hubs, Professional Services, and Success Plans.
Status pages are especially important for identity vendors because downtime directly impacts workforce access and customer login. Okta makes those links easy to find, which is a trust-positive UI pattern.
Security capability breadth as a trust signal
Okta’s product list itself conveys security maturity, including:
- Identity Threat Detection & Response and Identity Security Posture Management.
- Privileged Access Management.
- Identity Governance and Lifecycle Management.
- Secure Partner Access and Access Gateway.
By naming these controls, Okta demonstrates coverage across prevention, detection, response, and compliance—key evaluation categories for CISOs.
Third-party credibility
Okta reinforces trust with recognizable external validators:
- Gartner Magic Quadrant “Leader” language.
- Forrester study with a quantified 211% ROI.
These citations function as “borrowed authority,” particularly for conservative industries (public sector, financial services, healthcare) that are explicitly listed in the Solutions menu.
An improvement opportunity is making compliance artifacts more immediately discoverable from the homepage (e.g., SOC 2, ISO 27001, FedRAMP references if applicable), but given the presence of a Trust section and strong analyst proof, the trust stack is already robust.
Key terms: Trust, status transparency, Identity Governance, threat detection, Gartner Leader.
Detected tech stack
Tools and technologies we detected on Okta's site. Detection is best-effort and may be incomplete.
Scores
Our framework scores for Okta's website in terms of clarity, conversion, and trust. See our methodology for how we calculate these.
How clear the value prop and structure are.
How conversion-friendly signup and pricing are.
How well trust and compliance are surfaced.
FAQ
Okta’s homepage leads with a clear identity scope statement—employees, customers, and AI agents—then routes visitors into two platform paths: Okta Platform and Auth0 Platform. It reinforces credibility with quantified customer outcomes (e.g., 100M users, 1,500 apps) and analyst validation (Gartner Leader). Dual CTAs (free trial vs contact sales) match enterprise and self-serve buying behaviors.
Okta makes Pricing a top-level destination and pairs it with repeated “Start a free trial” and “Contact sales” CTAs. The surrounding product taxonomy (SSO, Adaptive MFA, Identity Governance, threat detection, Auth0) suggests modular packaging that varies by use case and scale, which is common for IAM. The approach supports quick evaluation while keeping enterprise quote paths available.
Okta’s social proof is unusually metric-driven. The homepage highlights named enterprise stories with specific results like 85% reduction in development labor, 250+ app integrations, and 480,000 users. It also adds third-party validation through Gartner’s 2025 Magic Quadrant Leader positioning and a Forrester study citing 211% ROI for Okta Identity Governance, strengthening procurement confidence.
Okta uses a two-track onboarding model: a 30-day free trial for hands-on testing and a contact-sales path for complex deployments. It supports onboarding with strong enablement surfaces—Support Center, product training, certification, professional services, and developer documentation. Status pages for both Okta and Auth0 are easy to access, which reduces operational risk concerns during evaluation.
Okta builds trust through dedicated Trust navigation, visible operational transparency (Okta Platform Status and Auth0 Status links), and an enterprise support footprint (support center, success plans, services). It also signals security depth via governance and threat modules (Identity Governance, Privileged Access Management, Identity Threat Detection & Response). Analyst recognition and ROI studies provide external validation for decision-makers.
The world's best-performing SaaS businesses share surprisingly similar patterns. We help you learn and apply them through our human-designed methodology, with AI-assisted research.